Not just another course library.
Thousands of free resources exist online. What's missing isn't content — it's structure, accountability, and real feedback. That's exactly what we built.
Live Lab Environments
Every concept is practiced in isolated, real-world virtual environments — not toy simulators.
Structured Progression
Courses are sequenced intentionally. No random jumping. Every module builds on the last.
Mentor Feedback Loop
Submit your lab work and get reviewed by a working professional — not an auto-grader.
Career-Ready Outcomes
Each path maps directly to real roles: SOC Analyst, Pen Tester, Red Team Engineer.
Explore our cybersecurity courses
Structured learning paths designed to take you from beginner to professional. Each course includes hands-on labs, real attack simulations, and practical projects used by security teams today.

Mastering Ethical Hacking
A complete, hands-on cybersecurity program that takes you from networking fundamentals to advanced exploitation techniques. Built for anyone serious about breaking into the security industry — no prior experience required.
Notify me on launch
Join 200+ students already on the waitlist
What you get in every course.
Every course ships with the same complete learning stack — not just videos, but a full system built to make you job-ready.
HD Video Lessons
Recorded by active practitioners. Real screen walkthroughs — not slide reads.
Browser-Based Labs
Spin up a live environment in one click. No VM setup, no installs. Just hack.
Graded Challenges
Every module ends with a real scenario. Submit your solution and get scored.
Mentor Reviews
Tag a mentor and get feedback from a working professional within 24 hours.
Cohort Community
Private Discord with your batch — peer study groups, Q&A, and job boards.
Verifiable Certificate
Shareable completion certificate recognised by our hiring partners.
Where do you stand today?
Pick the level that fits where you are right now. Each card filters the course catalog below so you see exactly what's relevant to you.
LEVEL 1
Beginner
LEVEL 1
Beginner
Start from zero
Understand how the internet actually works, build your first hacking lab, and develop the mindset used by ethical hackers.
LEVEL 2
Intermediate
LEVEL 2
Intermediate
Build real offensive skills
Move from theory into hands-on attacks. Learn web hacking, network exploitation, and defensive security techniques.
LEVEL 3
Advanced
LEVEL 3
Advanced
Operate like a professional
Advanced red-team techniques, exploit development, and real-world adversarial simulations.
Taught by people still in the field.
Our instructors hold active roles in their respective domains. They teach because they know exactly what employers look for right now.
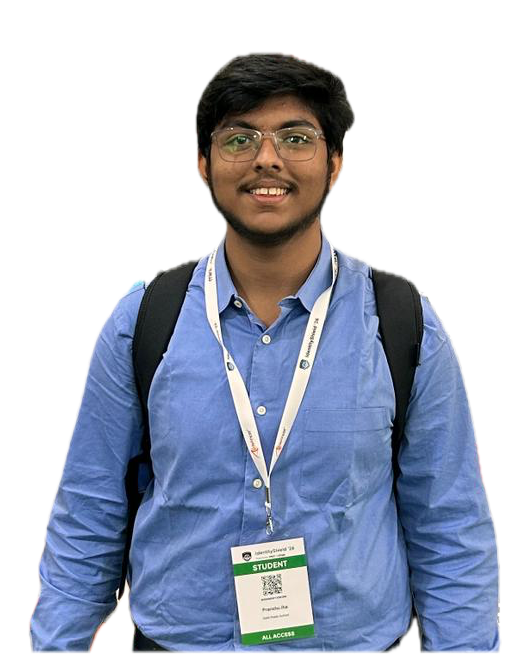
LEAD INSTRUCTOR
VERIFIED EXPERTPranshu Jha
Founder & Lead Instructor
Cybersecurity isn't about tools — it's about thinking like an attacker. My goal is to teach you how real breaches happen.
CRTA
3
Courses
500+
students
Real students. Real careers.
500+ graduates working at top companies. Their words, not ours.
This ERP revolutionized our operations, streamlining finance and inventory. The cloud-based platform keeps us productive, even remotely.
Implementing this ERP was smooth and quick. The customizable, user-friendly interface made team training effortless.
The support team is exceptional, guiding us through setup and providing ongoing assistance, ensuring our satisfaction.
Frequently Asked Questions
Find answers to the most common questions about our courses and learning experience.
Still have questions?
Talk directly with our cybersecurity instructors and get clarity before enrolling.
We took the first step. Now it's your turn.
We built this platform so no one has to figure out cybersecurity alone. From your very first terminal command to landing your first red-team engagement — every step is mapped, mentored, and battle-tested.
Trusted by 500+ learners ✦ 7-day refund · lifetime access · no hidden fees
Foundations
Networks, OS, basics
Offensive Skills
Pentesting & exploit dev
Defensive Ops
SOC, forensics, SIEM
Certified Expert
CEH, OSCP, CISSP ready
12K+
Engineers trained
94%
Job placement rate
48h
Avg. first skill cert
Joined this week
342 learners started their mission
